This is the original article about UFJJT1JJVEFJUkUK puzzle.

A recent afternoon, I was suddenly interrupted when typing away at my battle station in the office.
– “GadgetZZ got some mail, here you go.”
I stared at the package in disbelief and felt a sudden shift in the atmosphere. The package stood out like a sore thumb, and I got a feeling of something eerily familiar.
My first thought, as always, was skepticism and I started to inspect the package. Handwritten, addressed to GadgetZZ sent from Poland, stamped in Otwock and had no return address.
Inside was the package was a CD in a paper sleeve, on the sleeve was handwritten Base64 (immediately recognized as Base64 due to the string ending in = ).

Then on the CD itself was what looked to be parts of a Hex string written, either hinting that a part was missing or at that missing part, visualized by three dots deliberately placed between the groups.

If you didn’t make the connection yet, this both feels and looks like that mysterious CD that Johny received in 2015, just like this one it was from Poland and had Base64 scribbled on it. That took a viral turn and is known as 11B-X-1371. In case you missed it, that is a whole other rabbit hole.
https://gadgetzz.com/2015/10/12/this-creepy-puzzle-arrived-in-our-mail/
https://en.wikipedia.org/wiki/11B-X-1371

One thing is clear, I need to know, what is on that disc? Tempting, but I am not going to pop this in blindly. I started to prepare a machine with some basic digital forensics in mind that will be kept isolated and offline. As I chose my victim (laptop) and started to run dd 0 for good hygiene as I was digging around for a CD reader.
Suddenly there I was, laptop ready with the disc in hand. I pop the disc in and created a copy of the disk with FTK Imager.
Finally, we can have a look at the data.
Before I go any further, I will say that what was on this disc is beautiful and hard to do justice in words. What comes to mind is CICIDA puzzle, steganography and general feeling of something unknown hiding in plain sight. If you want to enjoy this mystery in its full glory without any spoilers, stop reading now. I will provide a link to a dropbox below to the image of this disk and all the raw data.
Dropbox link
Below I will share what I found on this disc, I am sure I missed plenty and I might have got some things wrong. This is my very first hands on experience with steganography puzzles. I got more caught up than I could’ve imagined and it did make me take a break from my recent obsession with lock picking. I will also try to keep short and not get too technical. This is what I found after hitting countless of dead ends, digging in Ghidra and getting completely lost, this was HARD.
Here we go!
Investigation
We have the Base64 on the disc sleeve “Q1JJVElDQUxMWUlNUE9SVEFOVAo=”, this translates to “CRITICALLYIMPORTANT”. The disc is in UDF format with the name “UFJJT1JJVEFJUkUK” which is Base64 that translates to “PRIORITAIRE”. Cyberchef was helpful here.
Here is an entropy graph of the disc from binwalk.

The disc has 6 files indexed, MESSAGE.001, MESSAGE.002, MESSAGE.003, MESSAGE.004, MESSAGE.005, MESSAGE.006. I could not find any hidden sessions of other data on this disc, someone else might have better luck.

Before I start going through the files, I ran exiftool on everything, digging around in unknown tags. I only found one thing that stood out, which can be found repeatedly in this dataset. The metadata has been scrubbed/altered. The date 02 feb 2002 02:02:02, is constantly present.

MESSAGE.001 and MESSAGE.002
Now let’s start with MESSAGE.001 and MESSAGE.002. These are text files, that at first glance looks to contain an identical poem but one file is larger than the other. I ran vimdiff on them and that showed MESSAGE.002 was riddled with non-printable characters, like zero width joiners.
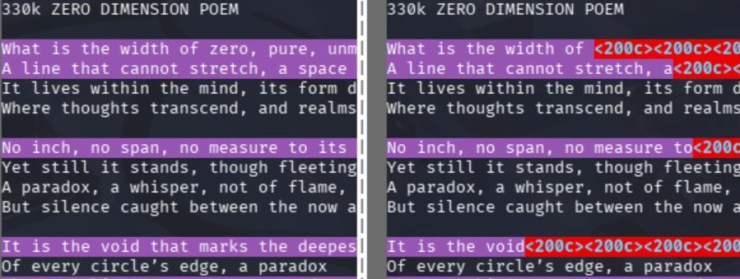
So, I opened MESSAGE.002 and stripped away everything except these anomalies, it wasn’t until later I made the connection that the poem itself was most likely a hint to these zero width joiners. I ended up with 24 groups that consisted of 8 characters.

There is 4 different characters used. Zero width joiner (U+200D), zero width non-joiner (U+200C), zero width space (U+200B) and pop directional formatting (U+202C). So 4 values, let’s try base4. I gave them values of 0-3 depending on their frequency, starting with 0 for the most frequent character. Voila, I got something?
00001110
00001020
00001011
00001002
00001030
00001033
00001003
00001023
00001033
00001012
00001003
00001020
00001001
00001021
00001032
00001103
00001021
00001103
00001020
00001001
00001003
00001023
00001011
00001010After some dead ends, I saw the pattern and assumed the consistency of the zeros in each group was just padding, so they are out. Now after translating the first groups of base4 to decimals, those numbers were in the perfect range for actual human friendly ASCII letters. Translating the whole thing revealed the following: “THEBLOCKOFCHAINSISHACKED”

MESSAGE.003
Let’s continue with MESSAGE.003. This one I did not spend very much time with; it’s public PGP key block. Maybe the creator is going to say hello at some point? Inspecting this key, we can see the date mentioned earlier again, but also the fingerprint for the key, it’s a perfect match for the partial string written on the CD.
06 FD 0A 02 E9 F2 3D 3A 32 01 AF 26 72 10 B8 6E 2E CA DE 92

MESSAGE.004
Moving on to MESSAGE.004. This file is also connected to MESSAGE.006 in my mind. MESSAGE.004 is a file with an unknown format and no extension, trying to look at the header you can see “v1.49…”, that didn’t tell me much.

The entropy of this file is towards the encrypted part of the scale. MESSAGE.006 is just a text file again, this time it is just poem, nothing hidden so the importance must be in the actual poem. It’s about a dog named Pico. A few searches later I have Picocrypt v1.49 installed on my machine, ran a few tests and I am certain that this is encrypted with Picocrypt v1.49, but it needs a password which I have not yet been able to figure out, yet.

MESSAGE.005
Lastly, we have the beast that is MESSAGE.005. This is where the rabbit hole suddenly got really deep, really fast. So far, I have been having a jolly time doing some minor ciphers and extracting what I deemed as valuable data, this file swept the carpet form under my feet, and I was not ready for it. This is a mpeg file complied with ffmpeg. There is no soundtrack, only one video track which visually looks like white noise and chaos.

This had me scratching my head, and I did some surface reading on hiding messages in videos. I hit some dead ends trying to find special frames by both extracting all the frames and only the I-frames, stacking all frames into 1 picture and so on.

The format mpeg, it’s a lossy format, that though relevant or not made me take a step back. At this point I had already figured out that video was in only black and white pixels flickering on/off, is this binary? Well wouldn’t you know, converting a first test part I think there is a pattern, which lead me to eventually extract the whole thing focusing on the macroblocks, 16×16.
Inspecting the output of the hacked-up Python script for this task, of course I expected nothing. I was met with an XZ header, unbelievable.

Because the data stream from the video ended a few frames before the actual end of the video, the last few frames were black. End of file will be broken and most archive tools will complain about this. There are some ways around this, I decided to keep going with Python and used lzma decompressor, ignore the missing end of file and forcefully open this thing.

Here we go, another file hiding inside. Immediately recognized as a JPEG file. I am in disbelief, both equally shocked and humbled by whoever created this thing and my own ability, both underestimated.

Let’s dive into the next layer; the QR code holds a valid onion address. There is no way this is a coincidence. Fired up TOR and took a peek. The first time I visited this address, it was offline but still valid. Only a few hours later, I thought “oh I just want to look at the http request/responses, maybe I missed something”. But to my surprise this time I see “200 OK”, well hello there, there now is a server alive on the address.
Final thoughts
It’s either here or before all my spoilers that I hope that someone more capable can continue to dig at this mystery. There are some strings, a date, encrypted file and a TOR site I feel like there is much left to learn. Finally, I will share my initial probing of the TOR site, I did not find much, but hey maybe that itself says something? Maybe there will be something completely different in the future?
Here is the normal response, content-length 0 and set ut UTF-8.

Sent a TRACE.

Finally here is the server throwing a 400, it was a from CONNECT I think.

All the best,
V






I agree, I don’t get same vibe from the contents as 11B-X-1371. This is cold and mechanical rather than emotional and artsy, right up my alley. Wow okey, thanks for the update, that is very intriguing I will go check that out this week for sure. Perfect timing as I just got back up on my feet.
I don’t believe that this is the same author, as he is not anonymous anymore… Or the first author is not the real author of original video. Nevertheless, the onion site is now working and I can see a short latin poem there…